Think how much of your business will go without it working and IT security. Cyber threats have increased rapidly and have prompted many companies to assess their preparedness. Thales, which provides security solutions, is experiencing a sharp increase in demand, particularly in the area of identity and access control (IAM).
The number of project orders and bids related to cyber threats has increased sharply in the past 12 months, says Mika Sonk, regional sales manager Sweden and Finland for access management products at Thales.
In the worst case, critical company data was hijacked and the attackers demanded a huge ransom.
Today we are seeing attacks from all connected devices. They can be phones, laptops, tablets, or servers. In today’s criminal networks, there are special operators, ransomware-as-a-Service (RaaS) and Initial Access Intermediaries (IABs) who search for holes in networks and sell information to criminals who commit intrusions.
Small businesses in particular
Many deal with the situation and secure work, while the most passive ones are exposed to increased risks. Today, the IT function is often outsourced, which makes the responsibility for security unclear. Especially weak is the access control function, which determines who can access in what conditions and under what conditions.
“Small businesses are particularly affected because they often downplay security issues and want simple solutions from outside IT vendors,” Sonck continues.
Provides user identity and access control security
Micah Sonic advocates a comprehensive security strategy. When a company decides to improve security, other considerations such as user roles and limited access rights according to roles follow. A strong personal identification should be available to every person with access.
Every company must secure their data, systems, and applications and decide who really needs access to each system. When someone terminates or changes information, access must be revoked immediately. Therefore, it is important that this be done in a simple way.
Advanced identity and access control systems, such as Thales Safenet Reliable Access (STA), used to protect cloud-based applications. There it is possible to create different roles with corresponding access rights and they can be changed at the touch of a button.
– The application can be accessed very precisely, for example, communicating with the geographical location of the user or the time of day. Biometric solutions such as fingerprints or facial identification increase security. The access control solution is scaled according to the size of the company and the cost is calculated per number of users, Sonck continues.
24/7 security services are becoming more and more popular
More and more people are using managed security services where access control is part of a more comprehensive security solution. The client’s network and system are monitored by 24/7 security analysts in the Security Operations Center (SOC).
The concept of SOC has been around for a long time, although it has become very popular in recent years. Identity and Access Control (IAM) is slowly becoming more popular, although specific business roles are still uncommon.
Security threats are constantly changing. Thales monitors developments and develops new protection methods. A hybrid IAM solution is currently being developed that controls access to both the cloud and on-premises data centers.
– Here we have a gem in which we believe a lot. Sonic comes up with the same product that guarantees access in both worlds.
Here You can get tips on how to move from older IAM to modern access management.

“Lifelong food practitioner. Zombie geek. Explorer. Reader. Subtly charming gamer. Entrepreneur. Devoted analyst.”










More Stories
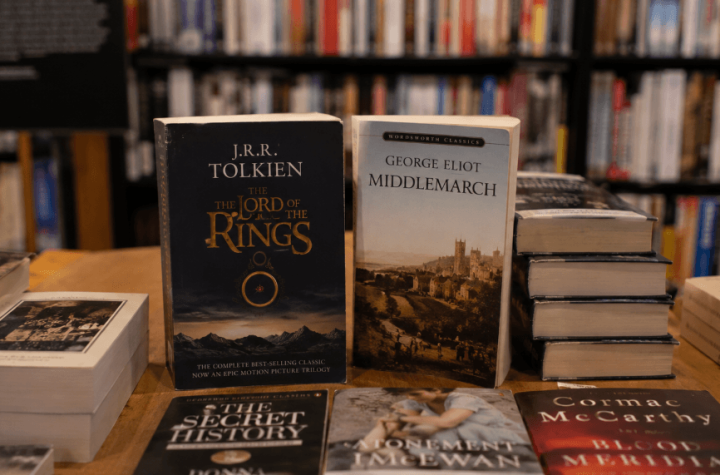
Readers Put The Lord of the Rings at the Top of the Greatest Novels List
Japanese Risograph Printer Helps Connect Global Artists Through Vibrant Independent Print Culture
Nintendo Clarifies Pricing Shift for Switch 2 Games as Digital Editions Become Cheaper